Seán Healy | Contributing Writer
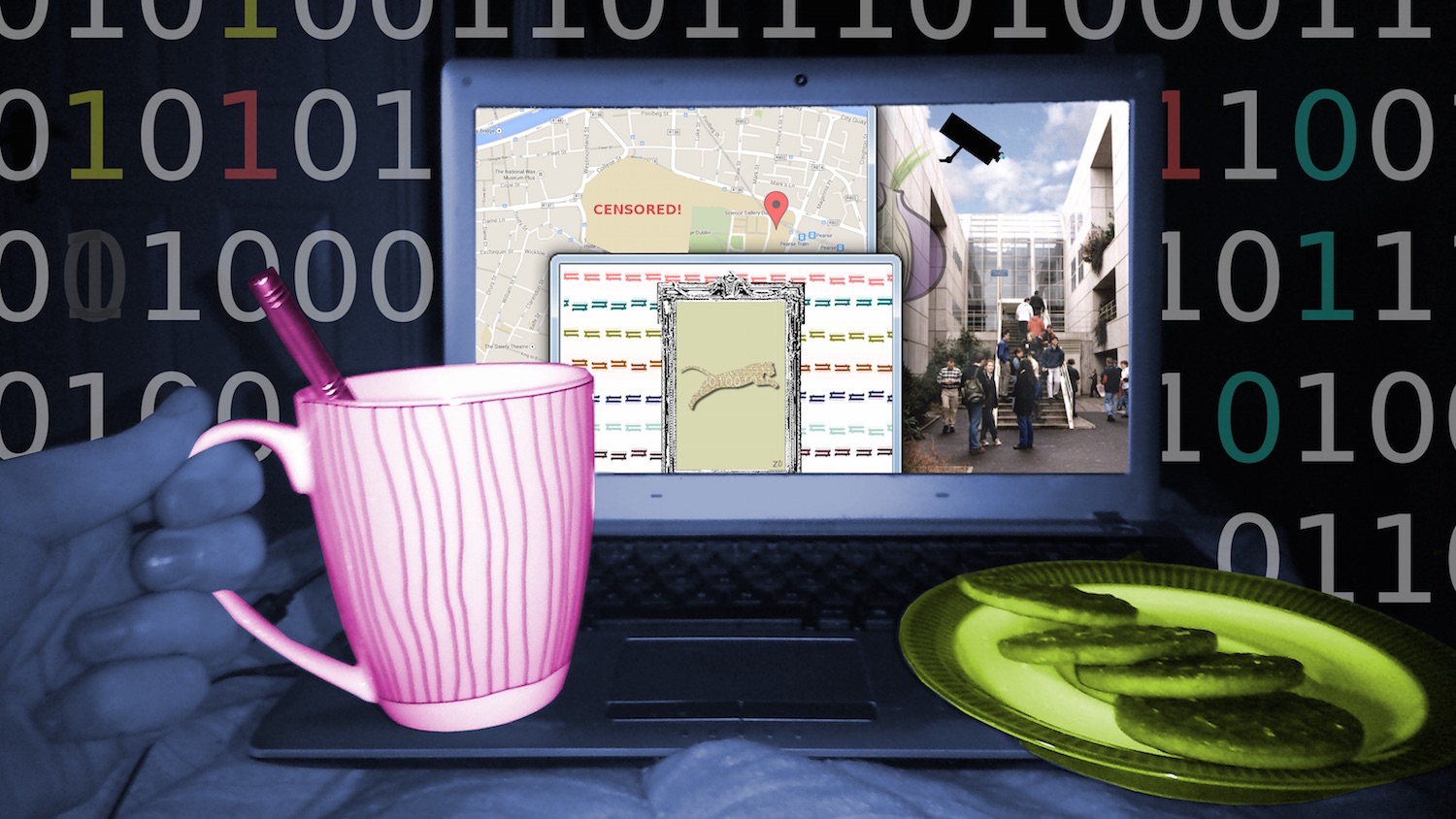
Over the past hundred years, we’ve seen many eras take flight, feathered or scaly. Our first bitter taste of modern warfare was followed by an era of diplomatic conflict unrivalled by any other history. With the science developed for military and patriotic intentions (on steroids during the Cold War), the dawn of the personal computer came unexpectedly premature, bringing with it the age of information. It was welcomed much more than the rebirth of surveillance and censorship in a new form – in the West, we now have less suspicion of a neighbour’s closeted communism, less of the inverse in former Soviet Russia, and on television, slightly less propaganda and a lot more nipples. Surveillance, this time, has not heightened our own wariness of people outside of power, but this seemingly lenient edition of spying has a new peeve: modern technology.
With the science developed for military and patriotic intentions, the dawn of the personal computer came unexpectedly premature, bringing with it the age of information.
In June 2013, Edward Snowden released information to the media, implying secret treaties, between members of UKUSA, with the end goal of implementing global surveillance. In August 2013, President Obama announced the formation of a “review group” that would report and brief, to him, on “communications technologies”, meaning the National Security Agency (NSA) would fall under his supervision, acting less as a separate entity. The US President insisted they weren’t listening to anyone’s calls. At a hearing in March 2013, James Clapper, director of National Intelligence in the US, when asked if the NSA collect information on citizens, responded, “No, sir.” The questioning Senator, Ron Wyden, continued, “It does not?” and Mr. Clapper clarified “Not wittingly. There are cases where they could inadvertently, perhaps, collect…” Three months later, Mr. Clapper released a statement contradictory to what he said under oath, revealing that the NSA collects data on the phone calls of millions of Americans. The lie was out, yet, government and organisation remained close-mouthed about the inner workings of the opaque NSA.
By tapping into someone’s internet connection, technically, anyone can get a list of the websites visited (provided they’re not https). In August this year, we witnessed the leaking of hundreds of private photos of various female celebrities. Two months later, 90,000 private photos taken by Snapchat users were stolen from the app’s servers and placed on the public web. Snapchat, used by many for romantic intentions, and the celebrity photos – not only private, but depicting all the women sexually, unveiled another layer of a growing canker of the information age. These images were thrust upon the world because the perpetrators knew there’d be a substantial, perverse audience.
How many accounts were hacked, recycle bins plundered? How many incidences of violated privacy took place to yield these rare images from the surrounding garbage of mundane selfies and family photos? If this is the visible, unauthorised surveillance we experience from single entities working out of their guardians’ basements, what more is there? With a government’s treasury and exclusion from the domain of the law, organisations like the NSA could be vast halls of white collars scrolling through your Facebook feed. To consider such an extent of surveillance becomes easier when we remember that, along with their diplomatic exemption, the technology is there, as is the motivation (NSA Motto: “Defending Our Nation. Securing The Future”). The funding is there too, and most importantly, the NSA have plenty of creeps to choose from in the employment pool.
Like a self modifying virus, or an algorithm posing a new problem with each perfect answer produced, surveillance is always matched by growing censorship.
Information technology may seem to be turning a bad egg. Like a self modifying virus, or an algorithm posing a new problem with each perfect answer produced, surveillance is always matched by growing censorship. If you post a breast feeding photo on Facebook, or the album from your recent charity ‘Dip in the Nip’, in most cases, the content is removed. How social network engineers developed systems to correctly differentiate a posterior from the crease between two knuckles is a mystery, but many would argue its value. Ten years ago, if a child with curiosity dangerous for their age typed something innocent that they heard a grown up say into Google, they’d meet a confusing wall of images predominately beige and brown in colour. Today, the result is similar, but a lot more clothed. With explicit results filtered, search for ‘sex’ and one of the images returned is a (female) wedding ring.
News of arrests over offensive Facebook pages circulates a lot more in 2014 than it did in 2004 (Facebook’s birth). Most would not contend that censorship, and investigation of pages entitled ‘[insert serious illness here] is fucking hilarious’ is a bad thing. With the rising cases of self harm, depression and suicide linked to cyberbullying, censorship is certainly more necessary now than it was in the era of silent film. Before Bebo and MySpace, after a school-day surrounded by bullies, a victim could go home and possibly return to a familial sanctuary, but now the kids exist as a hive-mind. The whole school, college or workplace is perpetually connected, and there’s less escape. In recent years, photos, mostly of women, some under-age, and generally depicting the person in a highly embarrassing and demeaning situation, have surfaced on numerous occasions on sites like Twitter, Reddit and 4chan, launching the victims to unwanted stardom overnight.
Jennifer Lawrence, speaking of her leaked, nude photos this year, stated simply, “It’s not a scandal. It’s a sex crime.” Poignant how many would relate to this description, and how many would ignore it, fortunately, the hive-mind can be empathic, especially in adulthood. Although Twitter administration can be slow off the mark when child pornography surfaces among the 500,000,000 tweets posted each day, users commonly come together and publicise the identities of those who shared the images, usually causing the culprits to willingly disappear from the internet. On Facebook, you can block your content from specific people / groups – the configuration of privacy settings are infinite. On most social networking sites, you can report things you find offensive. These described forms of censorship, enforced by the public, although historically echoing civilian eavesdropping, are beneficial to the masses.
Before Bebo and MySpace, after a school-day surrounded by bullies, a victim could go home and possibly return to a familial sanctuary, but now the kids exist as a hive-mind.
Censorship has its advantages as long as the public stands strong and recognises when things start to go overboard, for example, SOPA and PIPA in 2012. Surveillance has hidden advantages too. The NSA aren’t just interested in whether you’re guilty of spoiling Game of Thrones for your friends, or who that girl is to whom you keep opening a chat window but don’t have the guts to send a message. Their ominous, control-freak motto, “… securing the future,” is an attempt to indicate their self-professed good intentions. Indeed, they captured over 2,000 minutes of Osama Bin Laden’s phone conversations in the 80s (mostly heated arguments with his Mammy over what he’s doing with his life, I’d guess).
If I ever decide to start posting about TNT instead of tangled earphone cables or shortage of pens, and strange, sunglassed people start to arrive at my door asking questions, at first, I’ll feel a little hurt that they never liked my statuses to show me they cared, but I will concede that I feel safer too.
Last week, the Pirate Party (online piracy, not Johnny Depp) of Trinity College Dublin ran a tutorial on TOR browser. TOR is a programme that can be used to access the public web or the deep web. For suspicious characters who avoid surveillance and censorship like sunlight, the TOR network is a haven, but it’s also used by normal people, including those who simply oppose privacy violations in principle. TOR connects the user to the TOR network, where the user’s online request, be it downloading a web page, buying a gun or reading the latest wikileak, is passed through thousands of intermediate IP addresses. It is named ‘The Onion Router’ because, while using it, between the moment you click a link and see a page appear in front of you, your request has travelled through a vast network of layers, so those trying to track you can go suck an onion.
The TOR browser is not a land solely inhabited by cyber hippies and modern thinking innocents trapped within aggressively ruled nations. TOR is a platform. Like the Earth, it is home to all types, good and bad, and there is a lot of bad.
Many of those fighting censorship and surveillance take full advantage of TOR by surfing the deep web, a place where website domains are long, mostly gibberish, and rather than ending in .com, .ie, etc., end in .onion. The TOR browser is not a land solely inhabited by cyber hippies and modern thinking innocents trapped within aggressively ruled nations. TOR is a platform. Like the Earth, it is home to all types, good and bad, and there is a lot of bad. You can order heroin to your door like a pizza (for a higher price than the average Dominos, granted). You can fund extremist Islamic movements through Bitcoins. You can join forums to reflect openly on your most recent homicide. You can do all of this anonymously, uncensored, for free and in your pyjamas, on the deep web.
However, these are the expected negative outcomes when you create a community entirely free of identification and censorship. You only need to scroll through the average YouTube comments thread to see what some humans choose to become when offered a mask. Many applaud TOR for its service to a world in growing need of privacy. Yes, there are websites where stalkers share home addresses of their victims, but on the other side, victims can use TOR to communicate securely if a stalker has hacked their network.
In the same binary fashion as surveillance and censorship, which TOR attempts to tackle, the relationship between good and bad with this programme, and those like it, acts mutually, each side pushing against the other. Public opinion is kept tame, but cynical to the point that only a minority have even heard of the deep web.
An encrypted server, accessible only on the deep web, is a far safer place to store our naked selfies than iCloud. Despite this, as a medium against surveillance, it overcompensates, and thus, few would consider it a viable option for the future of the web. However, as the battle against purposeless surveillance and censorship advances, the privacy and technology used by TOR could be a step in the right direction.
Illustration by Seán Healy for The University Times